What is VNEC?
VNEC stands for Virtual Network Experiment Controller. VNEC allows the specification and execution of networking experiments in a virtual environment. Since several network experiments are either too sensitive (from a security point of view) or too expensive (due to required hardware) to be executed in a physical network, a virtual is often a wise alternative. VNEC allows the user to specify a network experiment and then automatically execute it in a VMWare virtual environment. An experiment is a network configuration (i.e., network topology and computer configuration) together with a set of tasks to be executed and their execution order. Click here for more details.
Where is VNEC developped?
VNEC is currently being developped in the Network Management and Artificial Intelligence (NMAI) research lab in the department of systems and computer engineering at Carleton University in Canada. The project is supervised by a Ph.D. student and two undergraduate students are actively developping VNEC. VNEC is designed in collabotation with the network security research group at Canada’s Communication Research Center (CRC) and is supported by the Talent First program of Carleton university.
What is VNEC used for?
VNEC is developped mainly for three applications:
- Gathering operating system (OS) signature for OS discovery tools
- Analyzing viruses spreading behavior
- Studying reaction of differnt OS against specific attacks
Documents
- Instructions
- Publications
- Gagnon F., Dej T., and Esfandiari B., VNEC – A Virtual Network Experiment Controller, Proceedings of the 2nd International DMTF Academic Alliance Workshop on Systems and Virtualization Management: Standards and New Technologies (SVM’08)
Downloads
- Release: VNEC-0.1 is available as a pre-alpha release
- Virtual Machines: VNECDispatcher1 is available on request. Please contact the authors.
Screenshots
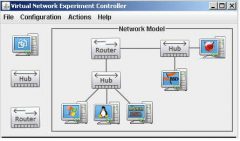
The screenshot below illustrates the network specificaiton module of VNEC. The user first construct the network topology by drag and dropping components (computers, hubs and routers). The component can be connected according to some rules. For instance,
- each computer as at most one connection
- computers cannot connect with other computers
- hubs can only connect with routers
- there should be at most 7 network segments
Finally, the user must assign a virtual machine to each computer.